Control 3rd-Party Payment Scripts Before They Put Card Data at Risk
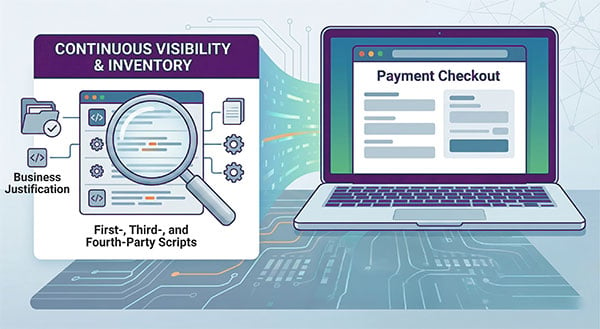
Source Defense helps ecommerce, security, and compliance teams control third- and nth-party JavaScript on payment pages, reduce eSkimming risk, and support PCI DSS 4.0.1 requirements 6.4.3 and 11.6.1.
Selected for Mastercard Start Path Security Solutions and trusted by more than 1,000 brands.
SEE HOW IT WORKS
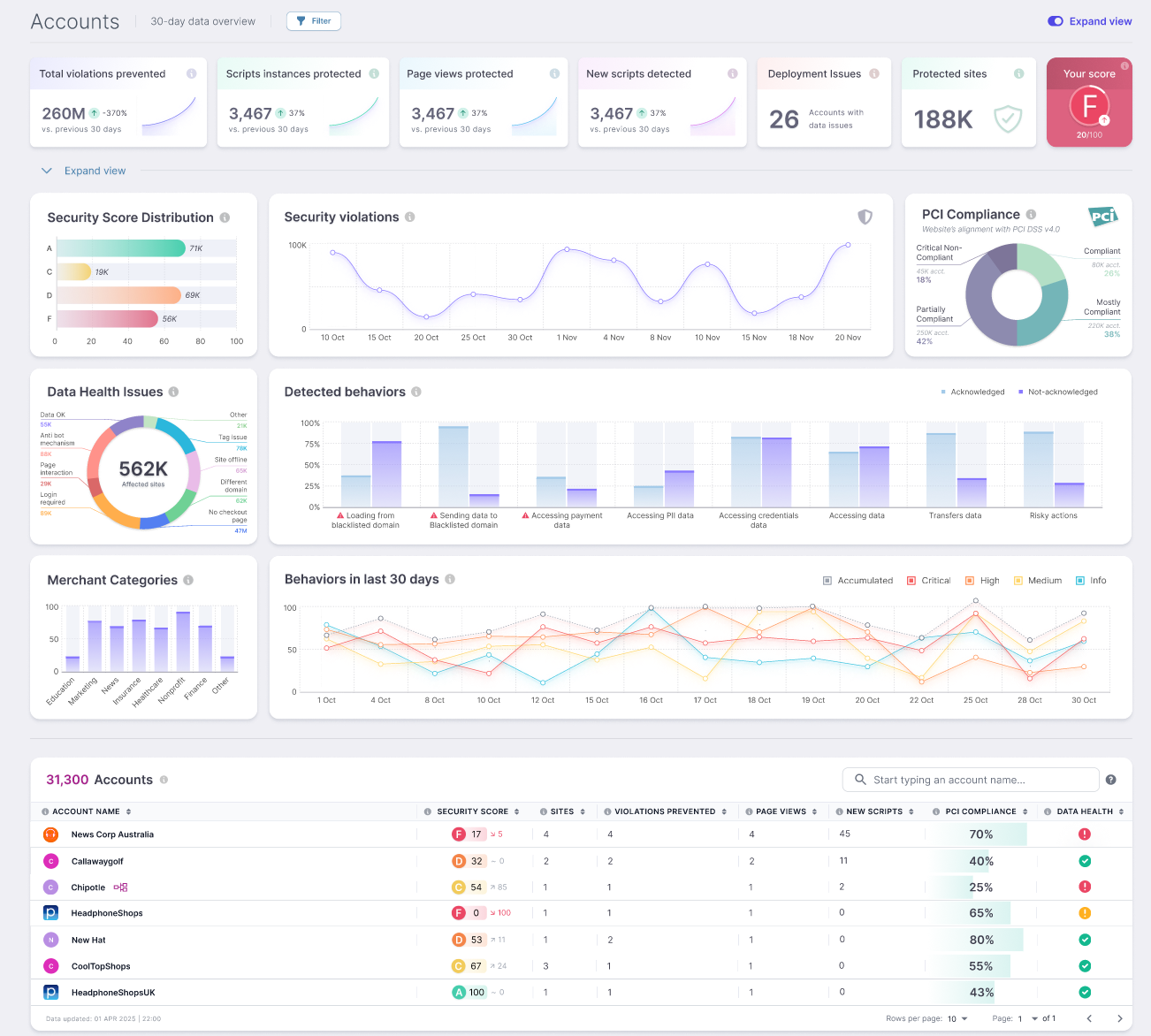
Modern checkout flows depend on analytics tags, tag managers, payment components, personalization tools, chat, fraud tools, and other third-party services. Those scripts, and the fourth parties they call, execute in the browser where they can read form fields, modify the DOM, capture keystrokes, and transmit data before it ever reaches the controls protecting your server-side environment.
That risk is real. Source Defense research published in Verizon’s 2024 Payment Security Report appendix A found 129,897 third- and fourth-party scripts across 7,075 websites, with 51,968 scripts on payment pages and 17,002 accessing PII. The average site had 18.37 scripts per page.
If your team is still relying on spreadsheets, manual reviews, CSP tuning, or periodic spot checks, you are trying to control a live browser environment with tools built for a static one.
See what Source Defense can do for you
Seeing is believing! Schedule a live demo with one of our product specialists at your convenience.
We will learn about your requirements, answer any questions you might have, and review ways Source Defense can help protect your business.
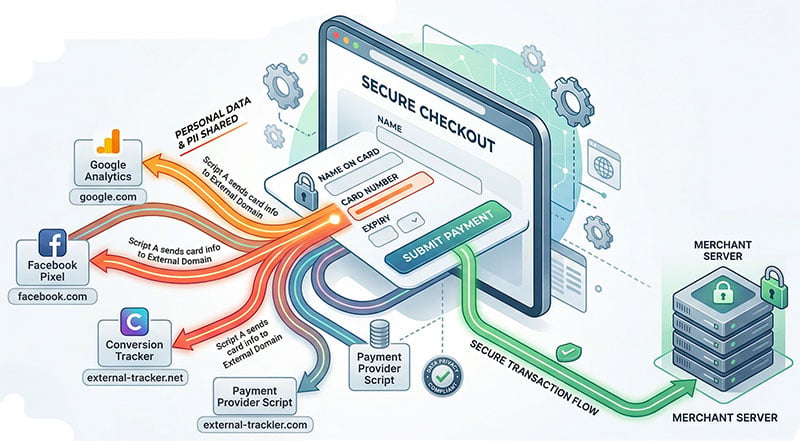
Get control over payment page scripts without breaking the customer experience
You can inventory first-, third-, and fourth-party scripts, see how they behave, monitor for changes, and apply policies that help prevent unauthorized access to sensitive data in the browser.
- Maintain an inventory of payment page scripts
- Document authorization and business justification
- Detect unauthorized changes to scripts and headers
- Monitor risky behavior across payment flows
- Control what scripts can read, write, or transmit
- Export evidence for assessor and audit conversations
Built for PCI DSS 4.0.1 requirements 6.4.3 and 11.6.1
Requirement 6.4.3 requires organizations to ensure payment page scripts are authorized, integrity-checked, inventoried, and justified. Requirement 11.6.1 requires mechanisms to detect unauthorized changes to payment pages and related security-impacting elements.
Support 6.4.3 with script inventory, authorization & justification
Support 11.6.1 with continuous monitoring and tamper detection
Monitor payment pages and related flows for unauthorized changes, suspicious behaviors, and unexpected script activity that could expose payment data or customer information.
![]()
Reduce manual compliance work
Replace point-in-time script reviews with ongoing visibility and exportable evidence. In the Hollywood Bowl case study, the security team expected PCI assessment closure to move faster because QSAs could accept Source Defense reports in lieu of manual tag reviews.

Selected for Mastercard to help combat digital skimming
Source Defense was selected to join Mastercard Start Path Program which is focused on advancing security and trust across digital commerce. The selection reflects a shared focus on reducing digital skimming risk, improving visibility into third-party script activity, and strengthening protection across the payment ecosystem.
Source Defense operates at the point where these risks exist: inside the browser, where payment page scripts execute and where card data can be exposed. Our platform is designed to control script behavior, reduce unauthorized data access, and support PCI DSS 4.0.1 requirements for payment page security.
Control script behavior, not just script sources
Allow lists and static controls do not solve the core problem. Third-party code changes frequently. Fourth-party dependencies appear without warning. A script can come from an approved source and still behave in ways you would never knowingly authorize.
VikingCloud highlights the complexity of CSP, its maintenance burden, and the risk of over-blocking or under-blocking legitimate resources.
Source Defense takes a behavior-based approach to client-side security. Our platform can monitor scripts in real time and apply policies such as monitored, isolated, redacted, and blocked.
That gives security and compliance teams something more useful than a passive inventory. It gives them a way to see risk and act on it in the browser, where payment page attacks actually happen.
Easier to deploy than most teams expect
Source Defense is designed to be deployed quickly without disrupting existing workflows. Implementation typically requires a simple two-line script, with out-of-the-box security and compliance policies that begin delivering visibility and control immediately. Ongoing management is minimal, often requiring only a few hours per month to maintain script oversight and compliance readiness.
The platform follows a structured path to PCI DSS 4.0.1 alignment, guiding teams through discovery, evaluation, onboarding, and verification without turning the project into a long, resource-heavy effort. This approach fits the reality most teams operate in, where the same people responsible for compliance are also managing tag changes, supporting digital initiatives, and responding to assessor requirements.
Independent reviews from Coalfire and VikingCloud support the applicability of Source Defense to PCI DSS 6.4.3 and 11.6.1.
Proven in complex payment environments
Hollywood Bowl Group
Hollywood Bowl Group implemented Source Defense to meet PCI DSS 4.0.1 requirements 6.4.3 and 11.6.1 across a complex ecommerce environment with extensive third- and fourth-party scripts.
The team gained immediate visibility into their payment page script ecosystem, removed the need for manual script reviews, and established continuous monitoring for unauthorized changes and eSkimming activity. Deployment was completed through a single JavaScript tag in their existing tag manager, with minimal effort from development and security teams.
READ THE FULL HOLLYWOOD BOWL CASE STUDY.
Nextiva
Nextiva took a similar approach, using Source Defense to close visibility gaps across its payment infrastructure and meet the same PCI requirements.
The company reports achieving full PCI DSS 4.0.1 compliance within one week, along with a complete inventory of third- and fourth-party scripts and a streamlined process for demonstrating compliance to assessors. Script monitoring, change detection, and reporting were automated, reducing the operational burden on security and compliance teams.
What you can expect from a demo
A Source Defense demo gives your team a clear view of what is actually running on your payment pages and how it behaves in the browser. You see every script in context, including third- and fourth-party dependencies, along with the actions each script can take and the potential impact on payment and customer data.
The session also walks through how scripts are inventoried, authorized, and documented to support PCI DSS 4.0.1 requirements. You can see how changes are detected, how alerts are generated, and how evidence is collected and exported for assessor review.
By the end of the demo, your team understands how Source Defense fits into your existing environment and how it supports both security operations and PCI workflows without adding unnecessary overhead.