Monitor Payment Page Changes Before They Become Incidents
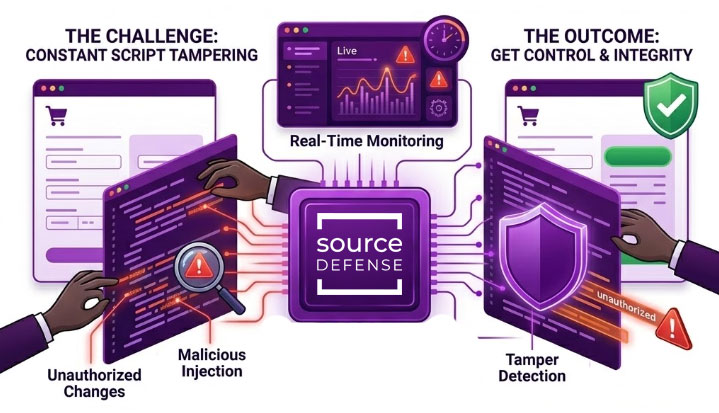
Modern payment pages depend on third- and fourth-party scripts that update constantly. Tag managers deploy changes daily. Vendors introduce new dependencies without warning. Attackers use the same paths to inject malicious code and skim data.
SEE HOW IT WORKS
Not every script change is a problem. The real issue is knowing which changes introduce risk, which ones affect payment page integrity, and which ones signal active tampering.
Source Defense Detect is built to identify unauthorized script changes, code injection, hidden form changes, and other behaviors that can indicate eSkimming or formjacking activity. It gives you visibility into what is running on the page, how it behaves, and where it may be putting payment or customer data at risk.
Source Defense Protect is about controlling what JavaScript is allowed to do in the browser. Protect uses behavior-based controls and real-time sandboxing to isolate scripts and prevent unauthorized access to sensitive data at the point of input. That makes it relevant when the goal is not just to detect script tampering, but to actively stop malicious behavior from succeeding.

See what Source Defense can do for you
Seeing is believing! Schedule a live demo with one of our product specialists at your convenience.
We will learn about your requirements, answer any questions you might have, and review ways Source Defense can help protect your business.
Built to Meet PCI DSS 4.0.1 Requirement 11.6.1
PCI DSS 4.0.1 requires organizations to detect unauthorized changes to payment pages and respond to them. That includes scripts, headers, and any component that could affect how payment data is captured.
Detect aligns directly to this requirement by continuously verifying page integrity and generating evidence your assessors can use.
- Continuous payment page integrity monitoring
- Real-time alerting on unauthorized script changes
- Detailed logs with timestamps and change history
- Exportable evidence for PCI DSS 11.6.1 validation
You are generating proof as part of normal operation, not after the fact.
Go Beyond Static Controls and After-the-Fact Alerts
Many teams rely on CSP policies, periodic scans, or SIEM alerts to detect script changes. These approaches are static, delayed, or incomplete.
They do not account for how scripts behave in real time, and they often miss the exact moment when data is exposed.
Detect operates in the browser, monitoring runtime behavior and identifying unauthorized changes as they occur. This approach aligns with how modern attacks actually work and closes the visibility gap left by traditional controls.
Designed for Payment Pages and Digital Supply Chain Risk
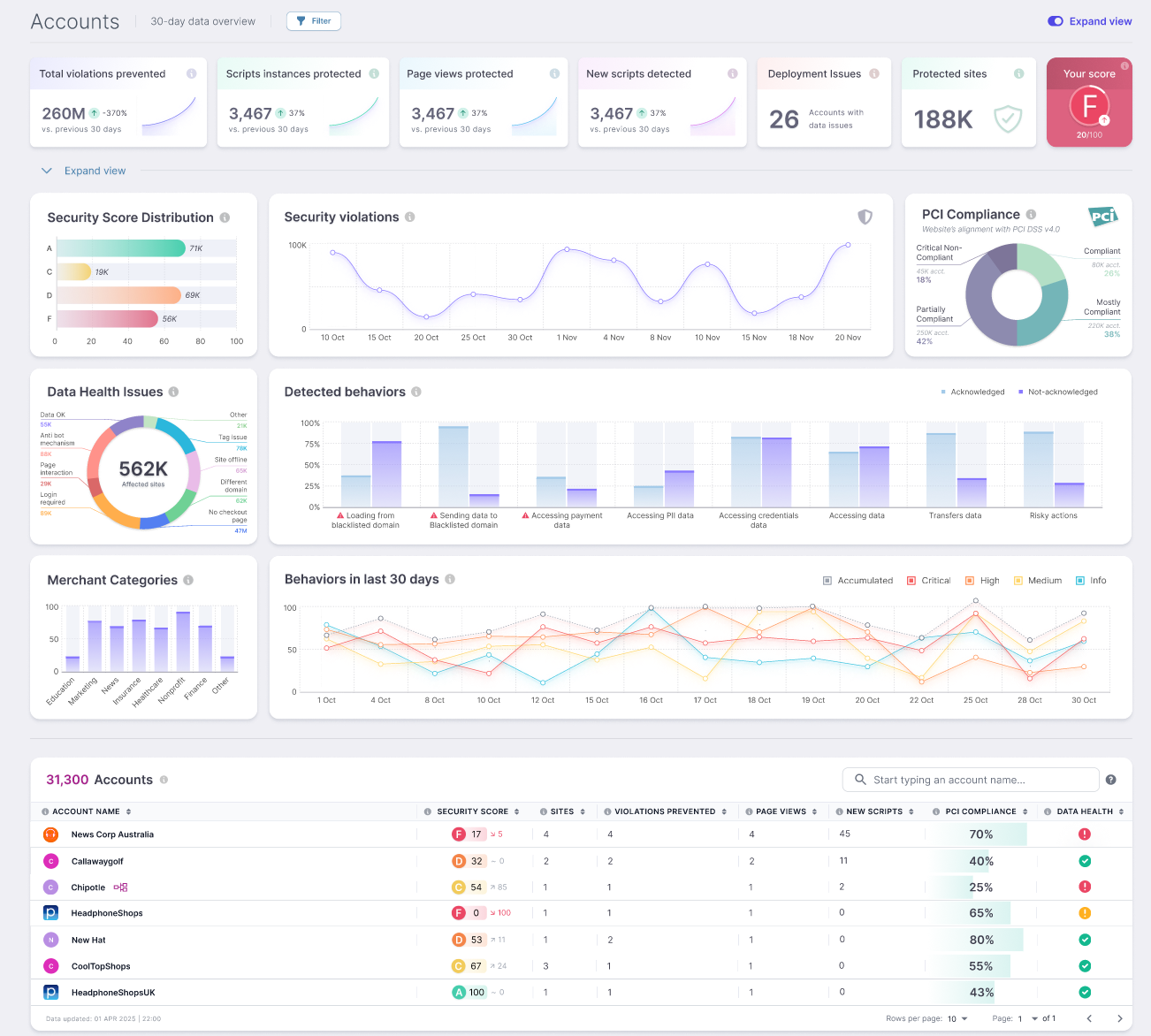
The risk is not limited to your code. It comes from the entire digital supply chain of scripts running in every user session. Source Defense Detect gives you a clear view of that ecosystem and how it changes over time, without adding operational overhead.
- Visibility into all scripts running on payment pages
- Tracking of third- and fourth-party dependencies
- Integration with existing security and compliance workflows
- Lightweight deployment with no impact on performance
Security, compliance, and digital teams all get the same source of truth.

Trusted by Mastercard to Protect Payment Pages Worldwide
Client-side digital skimming attacks are now a priority for card brands and payment ecosystems.
Source Defense was selected into Mastercard’s Start Path Program to help combat digital skimming and strengthen trust in digital commerce. That partnership reflects a shared focus on detecting script tampering, protecting payment flows, and improving visibility across the global web ecosystem.
See Unauthorized Script Changes in Your Environment
Most organizations do not realize how often scripts change on their payment pages or how many of those changes introduce risk.
A targeted assessment shows you what is running, what is changing, and where exposure exists today.
- Inventory of scripts across payment pages
- Identification of unauthorized or risky changes
- Detection of behaviors tied to eSkimming and data exposure
- Clear mapping to PCI DSS 4.0.1 requirements
Get Control Over Script Tampering and Payment Page Integrity
Unauthorized script changes are not rare events. They are a constant condition of modern web environments.
Detect gives you real-time script monitoring, tamper detection, and the evidence required to meet PCI DSS 4.0.1 without relying on manual processes or incomplete tools.
What you can expect from a demo
A Source Defense demo gives your team a clear view of what is actually running on your payment pages and how it behaves in the browser. You see every script in context, including third- and fourth-party dependencies, along with the actions each script can take and the potential impact on payment and customer data.
The session also walks through how scripts are inventoried, authorized, and documented to support PCI DSS 4.0.1 requirements. You can see how changes are detected, how alerts are generated, and how evidence is collected and exported for assessor review.
By the end of the demo, your team understands how Source Defense fits into your existing environment and how it supports both security operations and PCI workflows without adding unnecessary overhead.