Stop eSkimming Before It Reaches Customer Data
Protect payment pages and checkout flows from eSkimming, digital skimming, formjacking, and other browser-side attacks with the solution trusted by Mastercard.
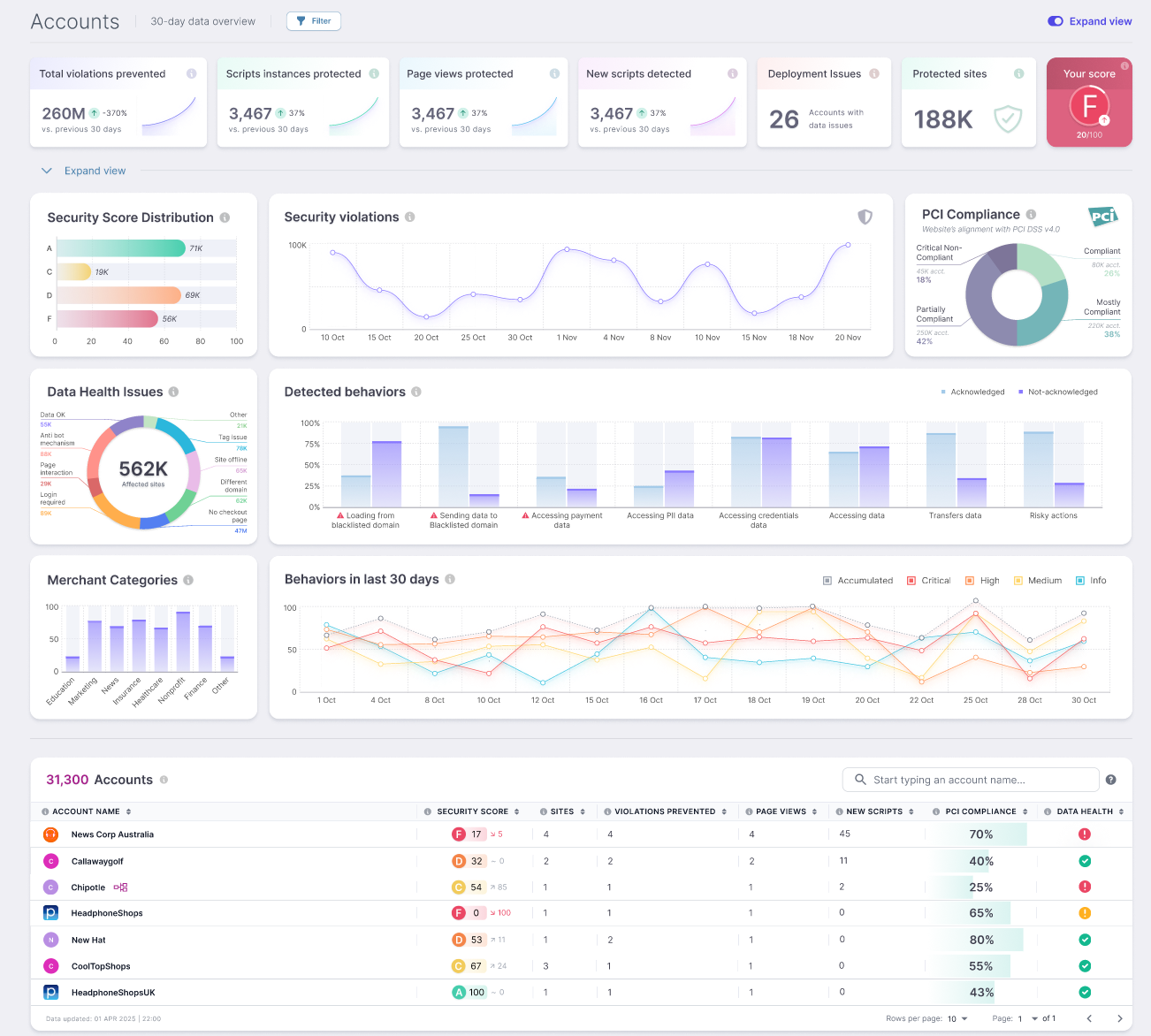
 Trusted by Mastercard to Help Protect Payment Pages
Trusted by Mastercard to Help Protect Payment Pages
Mastercard selected Source Defense for its Start Path program to help combat eSkimming across the global commerce ecosystem.
That matters because this is not a broad security platform forcing a payment page story onto a different product. Source Defense is built for the specific risk buyers in this market are trying to solve now: protecting payment pages and checkout flows from unauthorized script behavior in the browser.
For security teams, that means stronger control over what scripts can do. For compliance teams, it means a more practical path to supporting PCI DSS 6.4.3 and 11.6.1. For digital teams, it means protecting the website without stripping out the tools the business depends on.
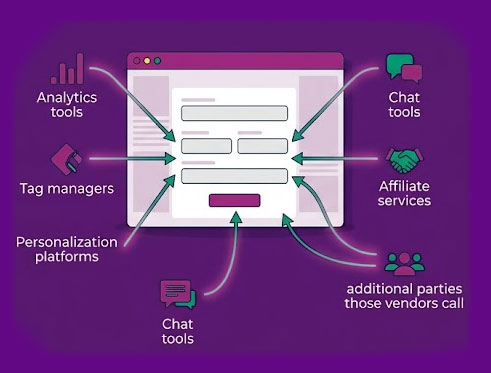
The Threat Is Already Running on the Page
Most payment pages rely on JavaScript from analytics tools, tag managers, personalization platforms, chat tools, affiliate services, and the additional parties those vendors call behind the scenes. That creates a browser-side attack surface that is large, dynamic, and often poorly controlled.
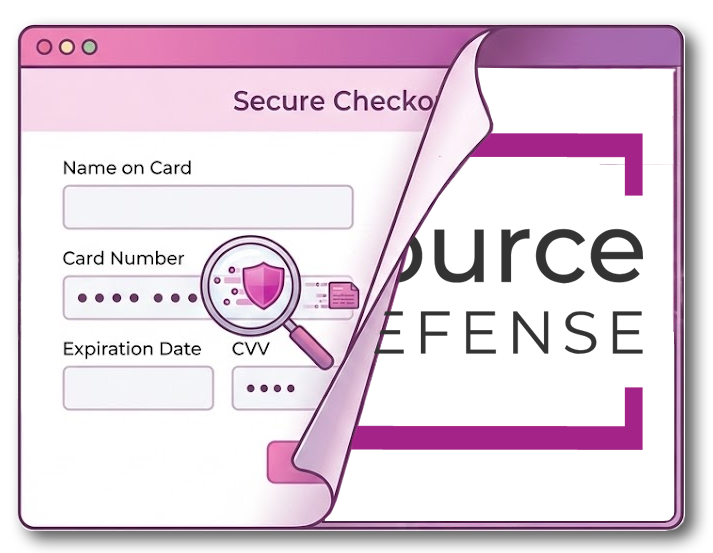
This is what makes eSkimming so effective. Attackers do not need to break through hardened server-side defenses if they can reach data while it is being entered into a form. When a script is compromised or behaves in an unauthorized way, payment data, credentials, and other sensitive information can be accessed before your existing controls ever get the chance to act.
That is the gap Source Defense is built to close.
Protect the Payment Flow, Not Just the Perimeter
Source Defense protects payment pages and checkout flows by controlling what scripts are allowed to do once they are running in the browser. Instead of relying only on static controls that struggle in dynamic environments, Source Defense focuses on runtime behavior. It helps you see which scripts are present, understand what they touch, track what changes, and apply policies that isolate, redact, monitor, or block unauthorized behavior in real time.
The point is to stop eSkimming attacks before data is stolen. With Source Defense, your team can:
- Maintain a clear inventory of payment page scripts and their dependencies
- Control what third- and fourth-party scripts can read, write, or transmit
- Detect unauthorized changes and suspicious behavior on payment pages
- Support PCI DSS requirements with cleaner evidence and reporting
Built for Real Websites, Not Idealized Ones
Many teams begin by looking at CSP or SRI. In practice, they often create maintenance overhead, operational friction, and breakage risk in environments where scripts change frequently and third-party dependencies are part of daily business.
That is the reality for most ecommerce teams.
Source Defense takes a different approach. Its behavior-based model helps protect payment pages without forcing the business into a brittle, high-maintenance process. Authorized tools can continue to function. Risky or unauthorized behavior can be isolated, redacted, monitored, or blocked.
This gives teams a more practical way to reduce exposure without turning payment page protection into a long engineering project.

Stronger eSkimming Protection and Clearer PCI Support
For many organizations, the pressure is coming from two directions at once.
They need to reduce exposure to eSkimming attacks, and they need to show how payment page scripts are being inventoried, authorized, justified, monitored, and checked for tampering under PCI DSS 4.0.1.
Source Defense supports both.
It helps teams maintain script inventory, document authorization and justification, monitor for changes, detect tampering, and export evidence in a format that supports assessor conversations. That makes it easier to connect security operations with compliance requirements instead of managing them as separate projects.
This is especially important for PCI DSS 6.4.3 and 11.6.1, where buyers are under pressure to show real control over what happens in the browser on payment pages and throughout the payment flow.
Easier to Deploy Than Most Teams Expect
Security teams do not need another platform that creates a long rollout, a pile of tickets, and a weekly argument with marketing or ecommerce.
Source Defense is designed to be lightweight to implement and low effort to manage. Deployment is straightforward, works in environments that rely on tag managers and third-party tools, and is built to preserve website performance and user experience.
That changes the conversation internally. Instead of asking whether the business can afford the operational burden of better payment page protection, teams can focus on reducing risk and moving faster toward a controlled, defensible process.
Proof From Real Customer Environments
Hollywood Bowl Group used Source Defense to gain visibility and control over its digital supply chain, eliminate manual script review work, and support PCI DSS 4.0.1 requirements 6.4.3 and 11.6.1. The company reported rapid deployment, unchanged website performance and conversion rates, and automated evidence that QSAs could use instead of manual tag reviews.
Nextiva used Source Defense to automate compliance work for 6.4.3 and 11.6.1, gain full visibility into third- and fourth-party scripts, and streamline assessor-facing reporting. The company reported full PCI DSS 4.0.1 compliance within one week of implementation.
These outcomes matter because buyers in this category are looking for proof that a solution can strengthen security, support compliance, and fit into real operational environments without slowing down the business.
Download the Hollywood Bowl Case Study
Download the Nextiva Case Study
The Better Way to Stop eSkimming on Payment Pages
eSkimming attacks target one of the most exposed parts of the modern website: the browser, where third- and fourth-party scripts can access data before traditional defenses ever get involved. Source Defense helps you protect payment pages where the risk actually lives. It gives your team a practical way to control script behavior, reduce browser-side exposure, support PCI DSS 4.0.1, and move forward without turning payment page security into a heavy manual process.
