Automate payment page script inventory for PCI DSS 4.0.1
See what scripts are running, what changed, and what your QSA will ask for.
SEE HOW IT WORKS
Can you prove control over your scripts?
Your payment pages depend on JavaScript from analytics tools, tag managers, payment services, personalization tools, and the fourth parties those vendors bring with them. That environment changes constantly, but your team is still expected to know what is running, justify why it is there, and show that changes are being monitored.
That is where most processes break down.
Verizon’s analysis of more than 7,000 merchant websites found 129,897 third- and fourth-party scripts, including 51,968 scripts on payment pages and 17,002 scripts accessing PII. The average site had more than 18 scripts per page.
For compliance teams, the requirements are clear:
- Maintain a current inventory of payment page scripts
- Justify what is there
- Identify unauthorized changes
- Produce evidence that stands up in an assessment

See what Source Defense can do for you
Seeing is believing! Schedule a live demo with one of our product specialists at your convenience.
We will learn about your requirements, answer any questions you might have, and review ways Source Defense can help protect your business.
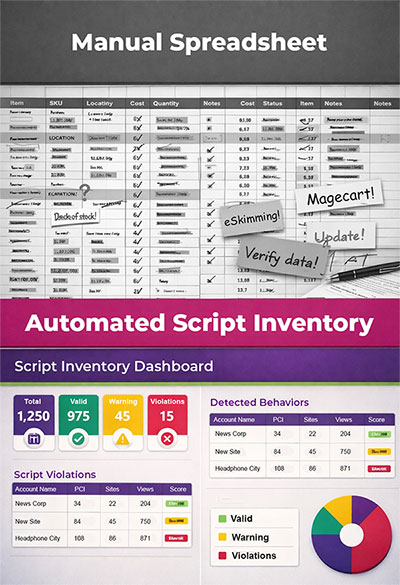
Manual tracking does not hold up in a live payment environment
Spreadsheets, browser exports, tag manager reviews, and one-time script assessments are all snapshots. The problem is that payment pages are not snapshots.
Scripts change. Pages change. Dependencies change. Teams change. Then the QSA asks for evidence as if the environment sat still the whole time.
That creates three problems at once.
-
Audit Friction: Teams spend too much time rebuilding script inventories, collecting screenshots, and trying to explain what changed since the last review.
-
Control Gaps: When changes happen between reviews, you are left with limited visibility into what is new, what shifted, and whether the current record is still accurate.
-
Security Exposure: Client-side threats such as eSkimming and Magecart take advantage of exactly this kind of blind spot, where payment page scripts operate outside the visibility of traditional server-side controls.
Common signs the current process is not working:
- No single source of truth for payment page scripts
- Limited visibility into third- and fourth-party dependencies
- Manual tracking of script justification
- No easy way to prove what changed and when
- Evidence gathering starts over every assessment cycle
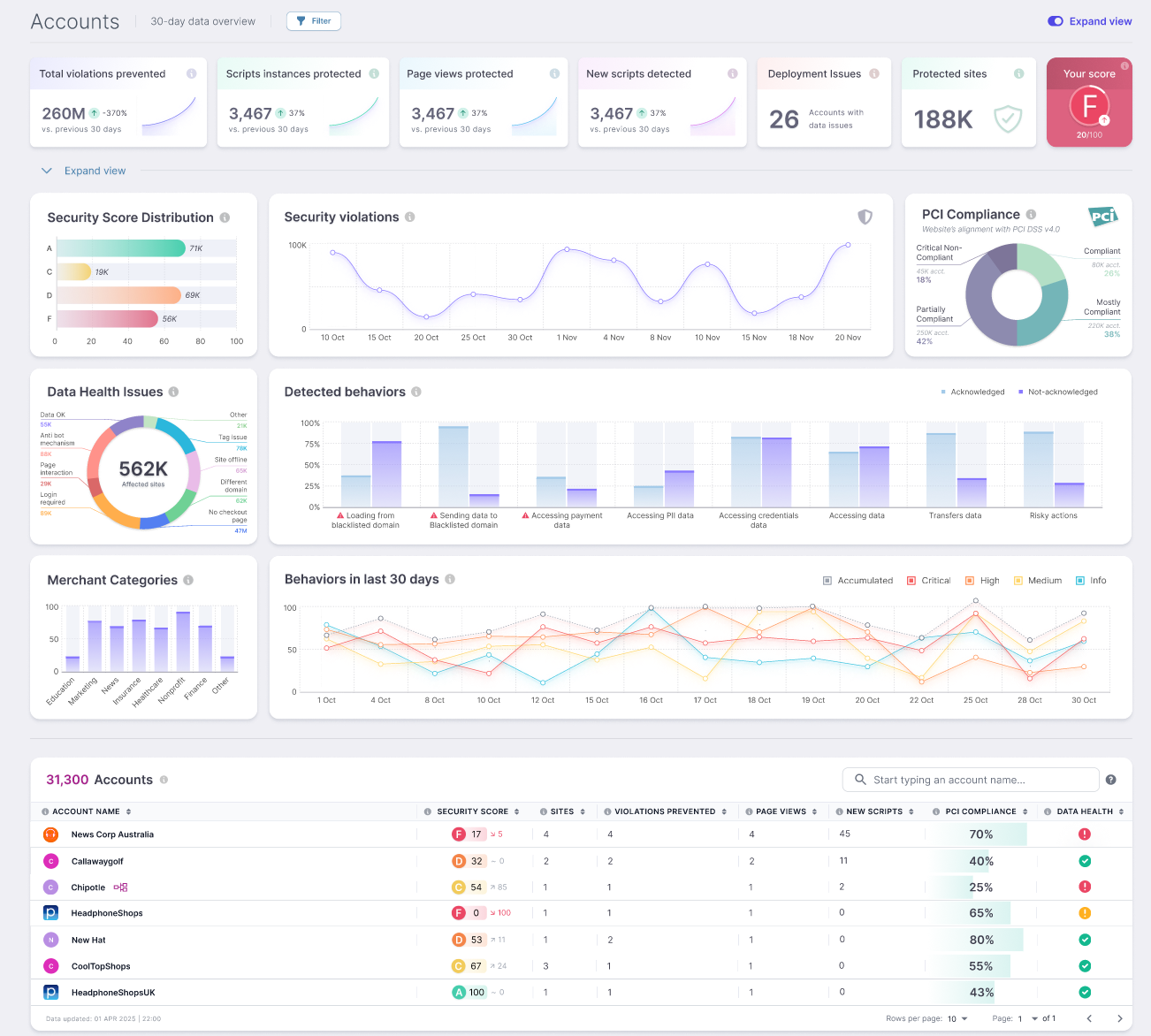
Source Defense Detect gives you a current record of payment page scripts
Detect helps compliance and security teams maintain a current view of what is running across payment pages and checkout flows without relying on manual collection.
Current Script Inventory
Change Visibility
Detect tracks script and page changes over time, helping teams see when something new appears or when expected behavior shifts.
![]()
Evidence Generation
Detect gives teams structured outputs they can use for reviews, assessments, and internal documentation instead of rebuilding the same story from scratch every time.
Built around the controls your team is being asked to prove
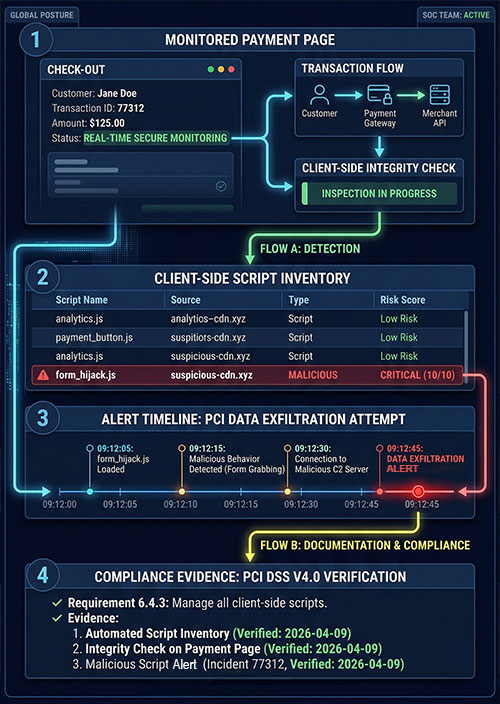
PCI DSS 4.0.1 introduced explicit requirements for client-side control over payment pages. Organizations are now expected to do more than assume their scripts are under control.
Requirement 6.4.3 requires organizations to:
Confirm scripts are authorized
Assure script integrity
Maintain an inventory of payment page scripts
Justify why each script is necessary
Requirement 11.6.1 requires organizations to:
Monitor payment pages for unauthorized changes
Detect tampering involving scripts and related elements
Alert when changes suggest risk to payment page integrity
How Source Defense Detect supports that work
Source Defense Detect helps teams turn PCI DSS 4.0.1 script requirements into a process they can manage.
It gives compliance and security teams a current record of the scripts running across payment pages and checkout flows, along with the context needed to review them, document them, and keep that record current as the environment changes. Detect helps teams by focusing on continuous script inventory, change detection, alerting, and evidence exports for client-side risk.
- Maintain a current inventory of first-, third-, and fourth-party scripts on payment pages
- Identify script and page changes tied to payment-page monitoring requirements
- Review script metadata such as source, category, page location, behavior, and history
- Support authorization and justification workflows tied to PCI DSS 6.4.3
- Export structured evidence for internal reviews and QSA discussions
- Reduce the manual work involved in ongoing compliance preparation, script review, and assessment support
Independent reviews from Coalfire and VikingCloud support the applicability of Source Defense to PCI DSS 6.4.3 and 11.6.1.
See what Source Defense can do for you
Seeing is believing! Schedule a live demo with one of our product specialists at your convenience.
We will learn about your requirements, answer any questions you might have, and review ways Source Defense can help protect your business.
What this changes for compliance and security teams
Most teams do not need more alerts. They need a process they can defend.
With Detect, your team has a clearer way to answer the questions that come up during reviews and assessments:
What scripts are currently running on payment pages?
Which scripts are first-, third-, or fourth-party?
What changed since the last review?
Where are those scripts active?
What documentation do we have for review and justification?
Instead of reconstructing the environment manually, teams can work from a current, structured record.
That reduces the scramble that usually happens before:
Assessor meetingsInternal control reviews
Remediation planning
Cross-functional handoffs with security, ecommerce, and engineering
Security leaders care about the same blind spot for different reasons
Even when compliance is driving the project, CISOs and security leaders are looking at the same issue from another angle. For them it's about meeting PCI requirements, closing a gap in visibility and controlling what happens on their website.
They want to know:
- Where browser-side blind spots still exist and which scripts are operating outside expected behavior
- Whether changes to payment pages can be identified quickly enough to reduce risk exposure
- How much operational overhead the solution introduces for already stretched teams
- Whether control can be strengthened without breaking site functionality or slowing down the business
This is where other approaches fall short. They either generate noise without context or require manual effort to maintain accuracy over time.
Detect gives teams better visibility into the scripts operating on payment pages and a more structured way to track changes over time. That supports PCI work while also giving security leaders better awareness of a part of the environment that traditional server-side controls do not fully cover.
Proven in live environments
Nextiva
Nextiva reported that compliance with PCI DSS 6.4.3 and 11.6.1 became fully automated with Source Defense, with clear visibility through the PCI dashboard. Deployment was completed within one week.
READ THE FULL NEXTIVA CASE STUDY.
Hollywood Bowl Group
Hollywood Bowl used Source Defense to gain visibility and control over its digital supply chain, eliminate manual script review processes, and improve PCI readiness without impacting customer experience.
READ THE FULL HOLLYWOOD BOWL CASE STUDY.
Third-party validation
Coalfire concluded that the Source Defense platform can offer value for proactive and reactive risk management tied to PCI DSS 6.4.3 and 11.6.1. VikingCloud found that Source Defense Protect, when deployed correctly, was capable of meeting those requirements.

Selected for Mastercard Start Path Security Solutions
Mastercard selected Source Defense to join its Start Path Security Solutions program as part of a broader effort to combat eSkimming across digital commerce. For merchants and payment teams, that is a useful signal: payment page script risk is now recognized as a payments, fraud, and trust issue, and Source Defense is focused on helping organizations address it with stronger visibility and control.
Fast to deploy. Easy to maintain.
You do not need another security project that takes months to implement before it produces anything useful.
Source Defense is built to be deployed quickly and managed without creating extra operational drag for compliance, security, or engineering teams. Detect gives teams current script inventory, change visibility, and evidence generation without turning rollout into a long internal project.
That matters because a control that is difficult to deploy often stays half-implemented, delayed, or stuck between teams. And in PCI, an unfinished control is still a problem.
With Source Defense, teams get:
Fast time to valueLimited burden on engineering
Cleaner outputs for assessors
A repeatable process instead of a recurring scramble

If your current script inventory process depends on screenshots and spreadsheets, it is time to replace it
Payment pages are dynamic. Your inventory process should be too.
Source Defense Detect helps your team:
- Maintain a current payment page script inventory
- Monitor for script and page changes
- Support PCI DSS 6.4.3 and 11.6.1
- Reduce manual evidence gathering
- Improve visibility into browser-side payment page risk