Detect Unauthorized Script Changes on Payment Pages in Real Time
Monitor script changes and detect tampering across payment pages and third-party JavaScript before data is exposed.
SEE HOW IT WORKS
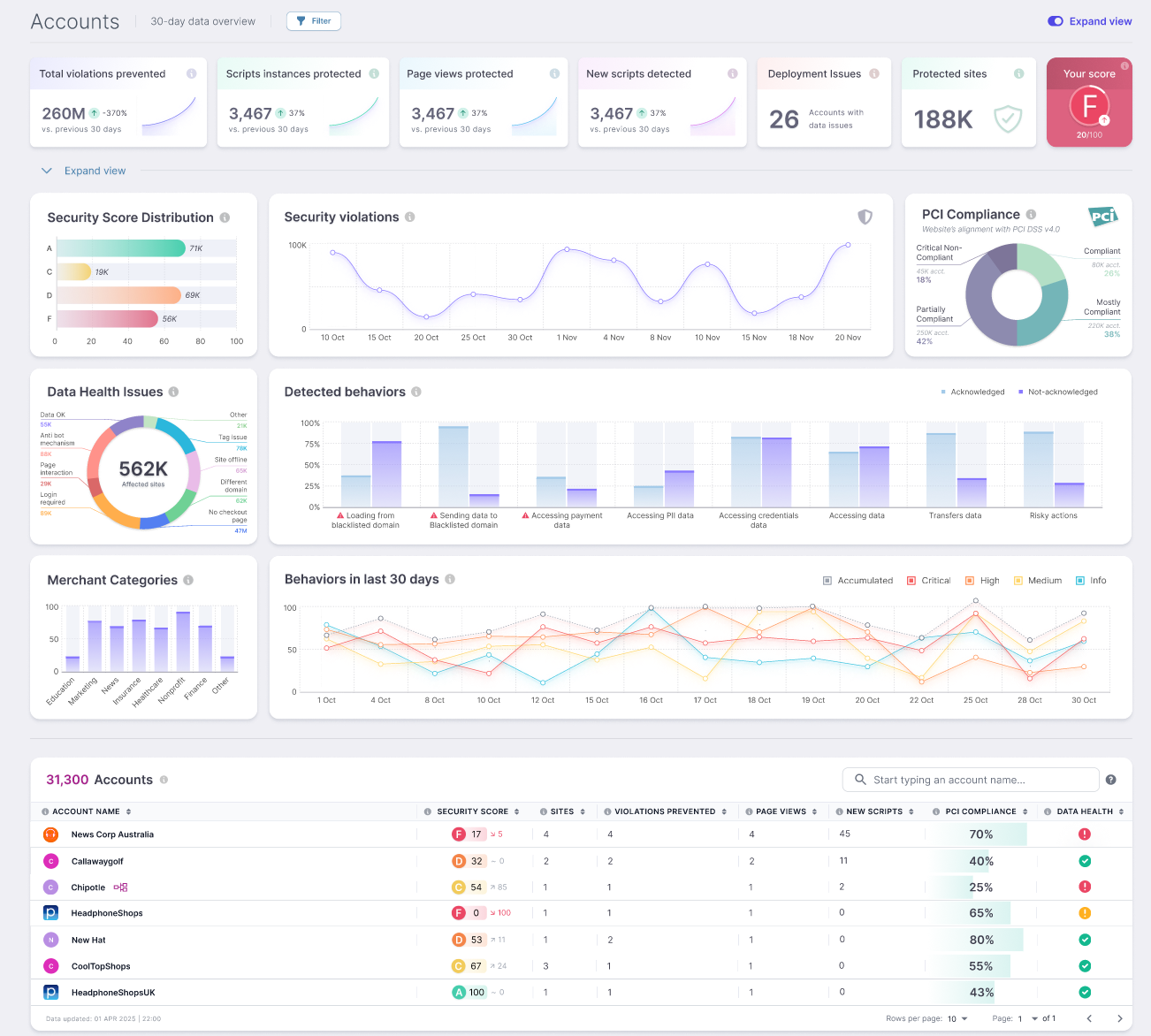
Most teams cannot see what changes inside the browser after a page loads. That is where payment page tampering, injected JavaScript, and digital skimming attacks can take hold.
Source Defense helps security and compliance teams detect script changes, monitor payment page integrity, and uncover unauthorized browser-side activity across first-, third-, and fourth-party code. Built to support PCI DSS 4.0.1 requirements 11.6.1 and 6.4.3. Trusted by Mastercard.
The problem is not just what scripts are running. It is what they change into.
A payment page can look normal and still be compromised. A trusted script can be modified. A third-party tag can introduce a new dependency. A hidden field can appear in the DOM. A form can be altered without anyone noticing until data starts moving somewhere it should not.
That is why script change detection matters. It is not enough to know a script exists. You need to know when it changes, how it behaves, and whether that behavior creates risk.
For teams searching for script change detection, website tamper detection, payment page tamper detection, or JavaScript integrity monitoring, that is the real job to be done.

See what Source Defense can do for you
Seeing is believing! Schedule a live demo with one of our product specialists at your convenience.
We will learn about your requirements, answer any questions you might have, and review ways Source Defense can help protect your business.
Detect what changed. Understand whether it matters.
Source Defense monitors browser-side activity across payment pages and checkout flows so your team can spot unauthorized changes before they turn into an incident or an audit problem.
It helps you:
- Detect unauthorized script changes on payment pages
- Monitor third-party and fourth-party script activity
- Identify malicious JavaScript changes and injected code
- Detect DOM manipulation tied to hidden fields, overlays, and altered forms
- Detect suspicious external calls and data exfiltration behavior
- Maintain script integrity monitoring for PCI workflows
This is how teams move from static reviews and periodic checks to continuous website security change monitoring.

Built for payment page tamper detection and PCI 11.6.1
PCI DSS 4.0.1 changed the standard for browser-side security. Requirement 11.6.1 focuses on detecting unauthorized changes to payment pages. Requirement 6.4.3 requires teams to inventory, authorize, and maintain integrity over payment page scripts.
Source Defense helps address both with continuous monitoring, script visibility, and evidence your team can actually use. Security gets clearer insight into what changed. Compliance gets a more defensible path to showing that payment pages are being monitored and managed.
That matters when the same team is trying to reduce risk, satisfy assessor questions, and avoid turning payment page monitoring into a manual process no one can keep up with.
Why this approach works better than static controls alone
Static controls can help, but they do not solve the full problem in dynamic environments. Payment pages change. Third-party code changes. Fourth-party dependencies appear without warning. Attackers take advantage of that movement.
Source Defense focuses on browser-side behavior and change detection, so teams can catch the kinds of tampering that simple file checks, allowlists, and manual reviews often miss.
That includes:
- Detect Magecart attacks before they become card theft
- Uncover formjacking behaviors on checkout pages
- Identify unauthorized third-party script changes
- Monitor script behavior tied to risky actions and data access
- Detect digital skimming attacks that operate inside the browser
For buyers looking for a website script monitoring tool, client-side tamper detection, or an ecommerce tamper detection solution, the goal is simple: find the changes that matter before they become exposed.

Trusted by Mastercard to Protect Payment Pages Worldwide
Client-side digital skimming attacks are now a priority for card brands and payment ecosystems.
Source Defense was selected into Mastercard’s Start Path Program to help combat digital skimming and strengthen trust in digital commerce. That partnership reflects a shared focus on detecting script tampering, protecting payment flows, and improving visibility across the global web ecosystem.
Designed for the way real teams work
Most organizations do not struggle because they lack security tools. They struggle because browser-side monitoring is hard to operationalize across compliance, security, engineering, and digital teams.
Source Defense gives teams a practical way to move faster without adding unnecessary friction.
You get a clearer view of the scripts running across payment pages, stronger visibility into script behavior, and a simpler way to spot changes that deserve action. Instead of chasing blind spots, your team can focus on real risk.
Stronger alignment between security and compliance
Security teams need to know what changed, what was introduced, and whether customer data is at risk. Compliance teams need to demonstrate that payment pages are being monitored and controlled in a way that supports PCI DSS 4.0.1. Instead of security investigating changes in one system and compliance documenting controls in another, both teams work from the same source of truth. Script inventory, change detection, and behavior monitoring are continuously tracked and tied directly to payment pages, making it easier to explain what is happening, why it matters, and how it is controlled.
Source Defense helps bridge that gap.
It supports the operational side of website integrity monitoring while making it easier to document payment page scripts, review changes, and support tamper detection workflows tied to PCI requirements. That gives both teams a cleaner story and a more credible posture.

See where your payment pages are exposed
You do not need another abstract security project. You need to know what is running, what is changing, and what could put payment data at risk. See script changes on your payment pages. Detect tampering earlier. Give your team a clearer path to PCI 4.0.1 readiness.